Strategic Whitepaper: Secure Zero-Trust Architecture for IBM i

Introduction
In an era of escalating cybersecurity threats, relying on perimeter defense is no longer sufficient. By employing a Zero-Trust Architecture (ZTA), we bridge the gap between the rock-solid reliability of IBM i and the modern web requirements of agility, performance, and global accessibility. By utilizing an architecture with NGINX as a high-performance gateway, an OIDC-compliant Identity Provider (IDP) such as Keycloak, and IceBreak as the native modernization engine, organizations can secure enterprise assets while enabling modern, high-velocity application development.
Infrastructure Diagram
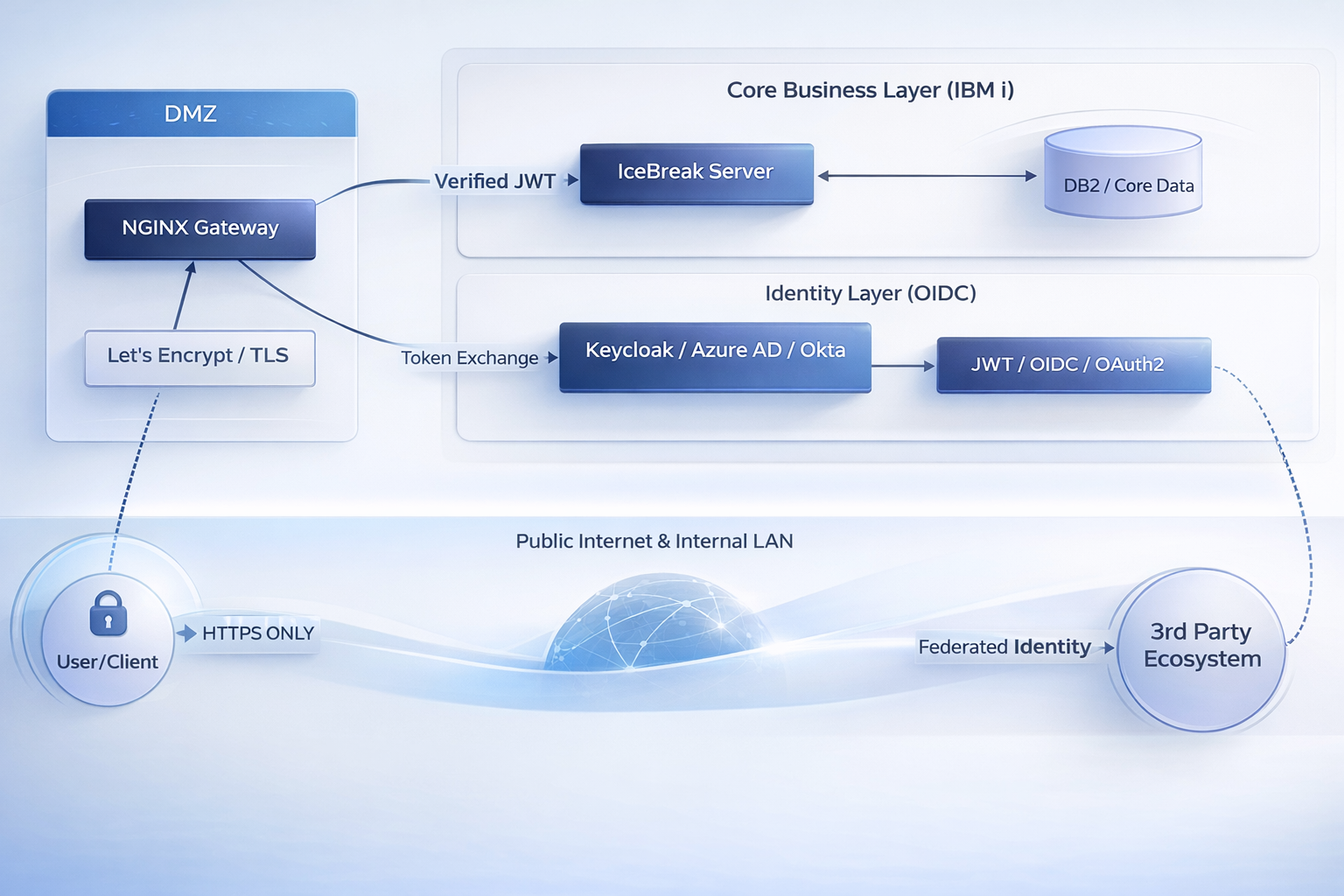
The architecture is designed to minimize the attack surface of the IBM i while maximizing throughput. All connections are encrypted and secured using industry standard https and digitally signed access tokens.
Understanding Zero-Trust (ZT)
Traditional security models follow a "Castle and Moat" approach. Once a user is inside the network (often via VPN), they are trusted. Zero-Trust turns this model on its head.
-
Never Trust, Always Verify: ZT assumes that the network is always hostile. Every request, whether originating from outside the office or from a desk inside the building, must be fully authenticated, authorized, and encrypted.
-
Least Privilege Access: Users are granted access only to the specific applications they need (e.g., an IceBreak-powered ERP module) rather than the entire network.
-
Elimination of Lateral Movement: By compartmentalizing services, if one user account is compromised, the attacker cannot "jump" from a web server to a database or a file share.
The Hardened Gateway
As the world's most popular web server and reverse proxy, NGINX serves as the critical "Single Point of Entry" for this architecture.
-
SSL/TLS Offloading: NGINX handles the computationally intensive task of encrypting and decrypting traffic. By negotiating and serving traffic at the gateway, the IBM i is freed to focus all its resources on business logic rather than on static file serving or cryptographic handshakes.
-
Advanced Traffic Control: Built-in Rate Limiting and DDoS Protection ensure that malicious actors or sudden traffic spikes cannot overwhelm your core IBM i system.
-
Security Through Abstraction: By acting as a reverse proxy, NGINX hides the internal IP addresses and structure of your IBM i network, making reconnaissance nearly impossible for attackers.
Automated Trust using Let's Encrypt
Securing every connection requires valid certificates. Let's Encrypt provides a globally recognized, industry-standard Certificate Authority (CA) that automates the entire lifecycle of security.
-
Zero-Touch Automation: Using the ACME protocol, this setup automatically requests, installs, and renews SSL/TLS certificates. This eliminates the risk of service outages caused by expired certificates and lowers costs.
-
Industry Recognition: Certificates from Let's Encrypt are trusted by all major browsers and security audits, ensuring a seamless and "green padlock" experience for all users.
-
HSTS Enforcement: This ensures that strict transport security is enforced, so a web browser can never downgrade to an unencrypted connection.
Modern Identity via flexible OIDC Integration
To achieve Zero-Trust, the stack utilizes industry-standard protocols. While Keycloak is a recommended open-source solution for centralizing user administration, other providers can be used; the architecture is designed for Provider Agility.
-
Standardized Compatibility: NGINX and IceBreak can support any OIDC-compliant system (such as Microsoft Entra ID/Azure AD, Okta, or Ping Identity).
-
OAuth2 & OIDC: These frameworks allow the infrastructure to verify who the user is and what they are allowed to do without exposing credentials to the application layer.
-
JWT (JSON Web Tokens): Keycloak (or your chosen IDP) issues a digitally signed JWT. IceBreak verifies this token locally at lightning speed, ensuring high performance without constant network round-trips to the IDP.
-
Keycloak integrates with AD or LDAP servers out of the box, enabling centralized management of corporate user accounts. By using plugins, integration with native IBM i users, Sitemule web users, or a custom solution is also possible. Furthermore, Keycloak has built-in support for Multi-Factor Authentication (MFA) and can integrate with other authentication mechanisms, such as Google, LinkedIn, GitHub, and more.
Ecosystem Extension through Third-Party Integration
A significant advantage of this OIDC-centric stack is its ability to extend your infrastructure's reach to external partners and services.
-
Federated Identity: By leveraging the authenticated OIDC session, you can allow third-party systems to "re-use" the existing user authentication, allowing your users access to third-party applications using their existing company credentials.
-
Secure Data Exchange: Partners can be granted limited, token-based access to specific IceBreak microservices, allowing them to interact with your IBM i ecosystem without requiring a separate login or direct network access.
-
B2B Collaboration: This enables a seamless experience in which external vendors or clients can securely access shared business processes, governed by the same central security policies.
IceBreak - Beyond Modernization to High-Velocity Development
While IceBreak operates as a bridge for existing IBM i programs to interact with the modern world, its capabilities extend far beyond modernization.
-
Modern Development Engine: IceBreak provides a high-performance runtime for building new native web applications and microservices on IBM i from scratch.
-
Native Performance: Built specifically for the IBM i architecture, it avoids the "tax" and memory overhead often associated with other technologies and programming languages, delivering sub-second response times for complex business logic.
-
Developer Agility: With built-in wizards, templates, and support for modern web standards (JSON, XML, REST), developers can build and deploy enterprise-grade services with significantly higher velocity than traditional methods.
-
Secured by Design: Being tightly integrated with the IBM i platform, the IBM i’s native security model is fully applied and supported.
The Strategic Advantage of a Single Point of Entry
By routing all traffic through a single NGINX gateway in the DMZ, the organization gains:
-
Universal HTTPS: All interactions are encrypted, removing "plain text" vulnerabilities within the internal network.
-
Decoupling Infrastructure: Users interact with mapped URLs, never accessing the IBM i file system directly. This prevents directory traversal and unauthorized file access.
-
VPN-Less Access: Hardened entry points with MFA remove the need for cumbersome VPN clients, lowering costs and improving the user experience while maintaining a superior security posture.
Strategic Benefits at a glance
|
Feature |
Strategic Impact |
|
Operational Efficiency |
Automated Let's Encrypt renewals and NGINX SSL offloading reduce manual labor and resource costs. |
|
Cost Reduction |
Eliminates VPN licensing and reduces IBM i CPU and memory use |
|
Ecosystem Reach |
Allows 3rd parties to securely reuse your OIDC authentication for integrated workflows. |
|
High Velocity |
Enables modern, rapid development of new services alongside legacy modernization. |
|
Security Excellence |
Implements ZTA to protect data at the source and eliminate lateral threat movement. |
Footnotes & Sources
-
Automation & TLS: Let’s Encrypt provides automated Domain Validation (DV). Source: ISRG.
-
Zero Trust Framework: See NIST SP 800-207 for standards on per-session verification. Source: NIST.
-
Performance: IceBreak's native architecture avoids JVM latency. Source: Sitemule Benchmarks.
FAQ & Takeaways
Why is Zero-Trust a better security model for IBM i than traditional perimeter defense?
How does a Zero-Trust architecture eliminate lateral movement risks?
Why is a single hardened gateway critical in Zero-Trust architectures?
How does IceBreak support Zero-Trust on IBM i without exposing core systems?
What strategic advantage does IceBreak provide beyond traditional modernization tools?
Engines
The Companies We Help
We provide solutions and services that support both standard and tailor-made systems for companies worldwide, serving a wide range of industries such as banking, finance, insurance, manufacturing, retail, logistics, and beyond. Let us help you - get in touch today!